INFRASTRUCTURE SECURITY
The measurement of the efficiency of operation of each organisation or company is not how it functions in the course of routine work, but how it manages in the time of chaos. Even the most experienced and prepared services are exposed to chaos related to:
- lack of sharing necessary information in the entire team,
- lack of coordination of tasks between individual units,
- lack of information on the use of technical and personnel resources,
- lack of access to reliable and verified information,
- lack of information on the progress of activities at individual sections of operation,
- lack of a possibility to exchange experience between individual units in critical situations.
AVISPON
– WHEN EACH DETAIL COUNTS
– WHEN EACH DETAIL COUNTS
Even the most advanced control systems will not prevent random events from occurring. The task of modern technical solutions is to support services in daily work in the scope of tackling even the most complex matters.
The Enigma’s offer includes the Avispon system created by our architects, computer specialists and engineers with a view to supporting a group of people professionally engaged in investigating criminal cases and other police-related events. This application is used in the case of occurrence of any crisis situation in an institution, failures of various type and scale, threat for the managed infrastructure, environment, employees or population, as well as in the case of image or information crises.
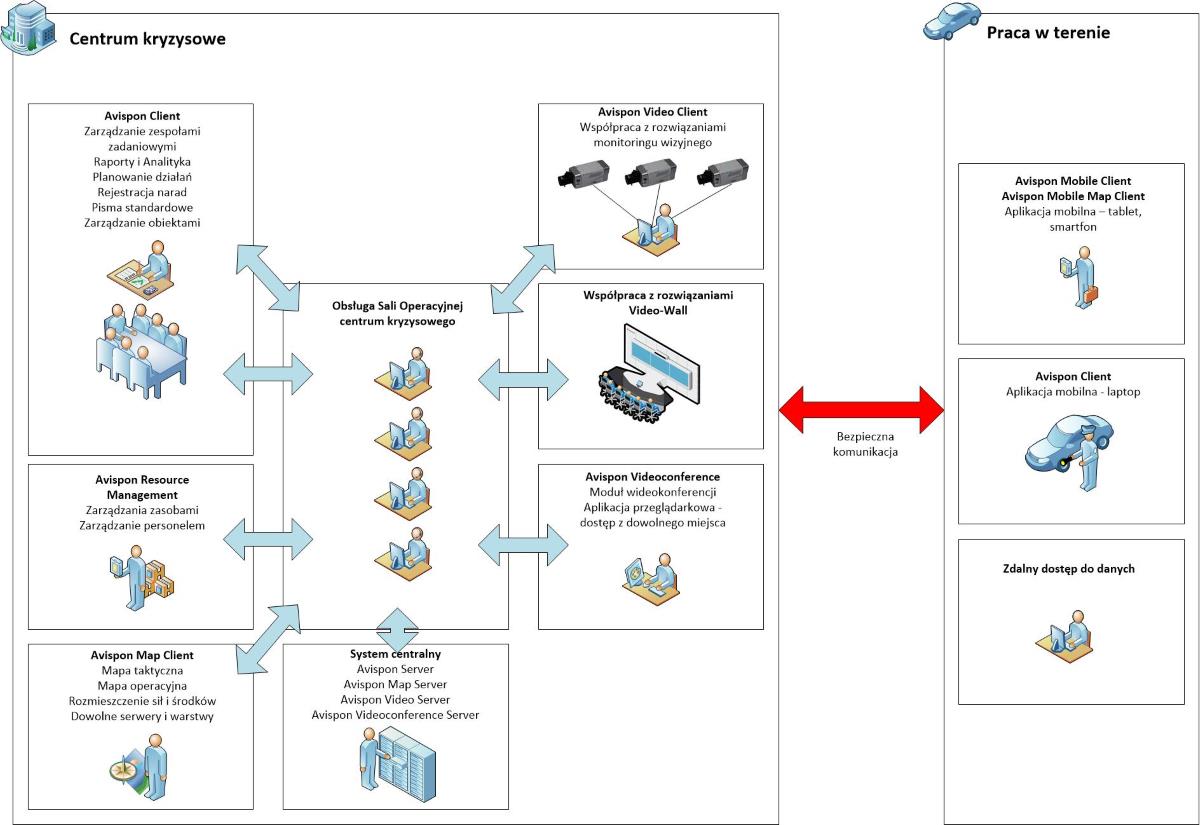
The system contains scenarios for reacting to particular crisis situations, sets of audit recommendations, good practices, and regulations used in handling incidents, as well as human and equipment resources, detailed maps of key areas and facilities specific for the given company. Flexible scenarios can be redefined during the crisis, depending on how the situation develops. The system uses mechanisms based on the GIS to position events, resources, and facilities on a tactical map. It offers the ability of working with or even controlling CCTV and mobile camera systems, has a built-in videoconference module for groups, teams, and external consultants, with the possibility of sharing resources (desktop, files, images and documents). High level of security is guaranteed by the possibility of controlling authorisations based on roles performed in the team dealing with the given incident, integration with an authentication system based on Active Directory, and integration with e-signature systems.
MODULES
- effective assigning of tasks to teams,
- control of task completion,
- reports supporting decision making,
- ability to introduce incident-related information,
- automation of basic processes,
- access to key information for authorized team members,
- context information as assistance in completing tasks,
- dynamic mode – voice notes instead of manually entered data,
- immediate messages to all users.
- ability to define any reports supporting the management of an incident,
- overview and detailed reports concerning task completion,
- reporting progress in completing the assigned tasks.
- stenographic support,
- dynamic mode – recording the meeting and its playback in the system,
- ability to create tasks based on decisions made during operational meetings.
- ability to define scenarios to react to various crisis situations,
- flexible scenarios can be redefined during the crisis, depending on how the situation develops,
- implementation of audit recommendations, good practices, and regulations in the incident handling process.
- granular system of defining and introducing objects,
- ability to define objects with any properties/attributes,
- ability to define links between objects reflecting the interdependencies existing in the real world.
- built-in mechanisms using the GIS to position events and objects,
- tactical map presenting the arrangement of resources and personnel,
- easy searching for and filtering of objects,
- access to archive data specifying the locations of particular objects.
- management of camera control mechanisms,
- management of stationary cameras, field reconnaissance vehicles, cameras on drones and off-line images,
- use of external camera systems and object identification systems.
- ability to send parameters to external systems,
- working with external work-support mechanisms.
- full warehouse support for task teams,
- support for work time and efficiency monitoring.
- creating rooms for discussions for particular incidents, teams, and groups,
- support for videoconferences attended by external consultants,
- ability to share local resources: desktop, files, images and documents.
- role-based access control (RBAC) reflecting the structure of the team, defined for each incident,
- team structures management – authorizations and subordination,
- integration with an authentication system based on AD,
- integration with e-signature systems.